https://www.kqed.org/mindshift/49454/anxiety-is-taking-a-toll-on-teens-their-families-and-schools
Anxiety is increasingly becoming a serious issue for American teens. Sixty-two percent of incoming freshman surveyed by the American College Health Association said they’d experienced overwhelming anxiety the year before, up from 50-percent in 2011.
it’s often the more affluent families who find the problem most baffling.
Denizet-Lewis goes on to write that many people assume teens feel this stress because of helicopter parents who do too much for their kids.
+++++++++++++++++
more on contemplative practices in school in this IMS blog
https://blog.stcloudstate.edu/ims?s=contemplative
You’ve Been Hacked! Explaining Cybersecurity to Students in an Interconnected Era
By Jacob Batchelor 06/01/17
https://thejournal.com/articles/2017/06/01/youve-been-hacked-explaining-cybersecurity-to-students-in-an-interconnected-era.aspx
Here’s an easy way to explain IoT hacks to students:
- A hacker accesses a device, like a webcam, through its internet connection. Devices with weak security or easy-to-guess passwords make easy targets.
- The hacker can then infect the device with malware, a type of computer virus that takes control of a device.
- The hacker now has a number of options. He or she can use the device to spy, infect other devices or attack a target like the servers (centralized computers that store network data) targeted in the October 2016 attack.
- Research the manufacturer. Are they reputable? Have they previously been hacked? Big, established companies based in developed countries are usually the safest.
- Read up on security features. Is the device password-protected? Can you set your own password? If so, make it a strong password that uses numbers, letters and symbols — avoid common words or phrases.
- Regularly check for updates. Good companies will regularly update the software on their devices to protect against vulnerabilities.
- Ask yourself — do you need it? Make sure internet-connectivity is something you really need on the device you’re using. In many cases, internet-connectivity is not necessary for the device to function properly.
a few tips that students can use to protect their privacy while using smartphones:
- Research apps before signing up for them. Is it from a reputable developer? Has it had security issues in the past? Use the same approach as when researching IoT devices.
- Look over the terms of service. What information does it require? Does it track or store your data? Can the developer sell your information? All of these questions are important to consider.
- Be careful when linking apps to your social media accounts. Giving apps access to your social media accounts makes them vulnerable to hacking. Is there a good reason for the accounts to be linked? Can you sign up without linking to a social media account?
- Use two-factor authentication. Two-factor authentication requires authorization beyond a password when using unrecognized devices such as entering a code sent to your cellphone. As apps allow, be sure to use two-factor authentication which will make it more difficult for hackers to access the information stored in your apps.
++++++++++++++
more on hackers in this IMS blog
https://blog.stcloudstate.edu/ims?s=hacker
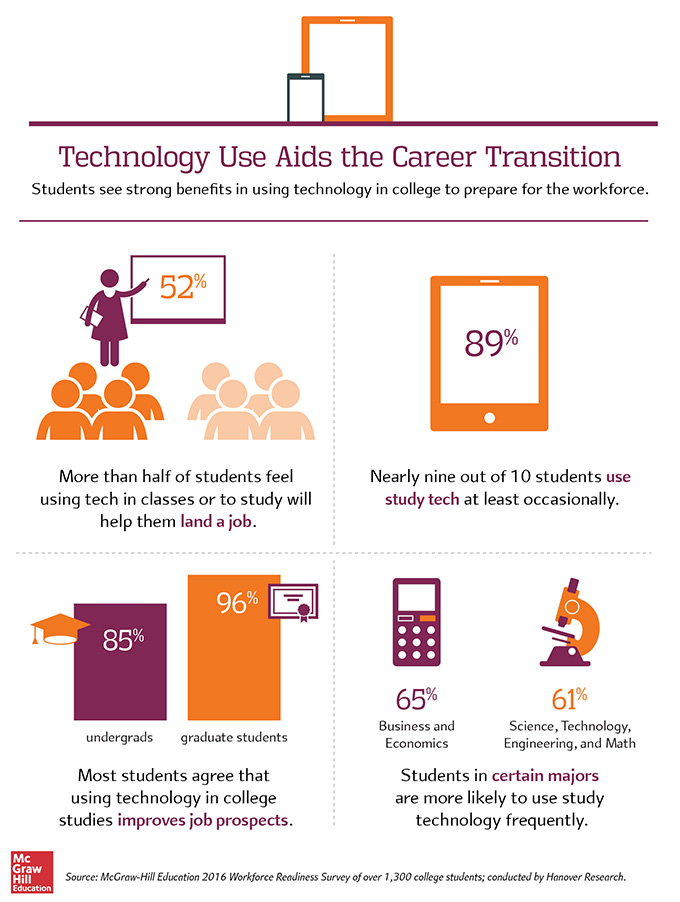
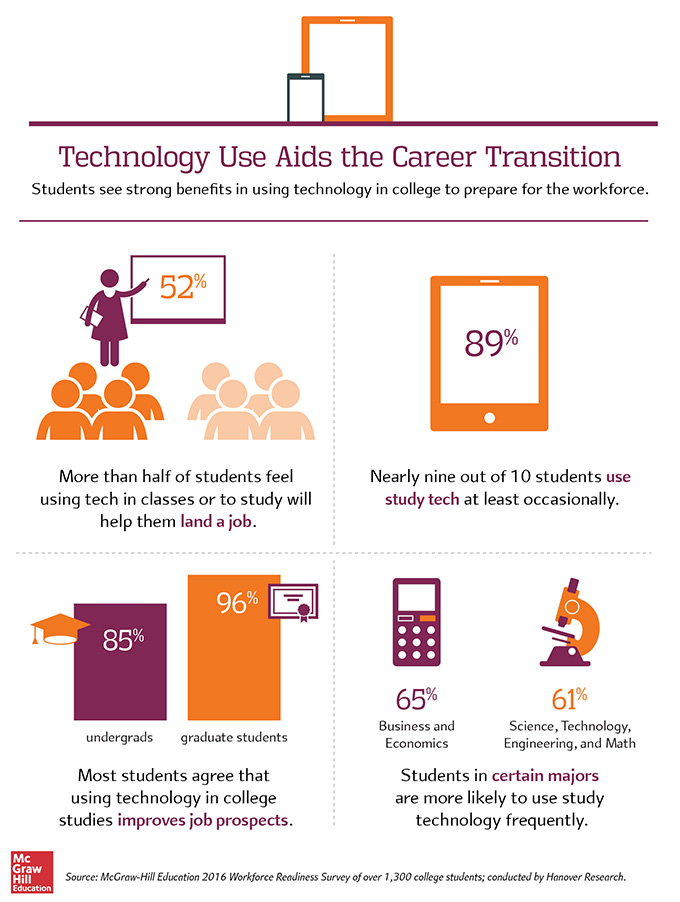
Technology Use Boosts Students’ Confidence in Their Job Prospects [#Infographic]
Graduating seniors believe the technology skills they’ve acquired in college will help them start their careers.
The finding is good news for colleges and universities focused on digital transformation — whether that means implementing new classroom technologies,
transitioning services to the cloud or building out the back-end infrastructure needed to support students’ increasing
bandwidth demands.
+++++++++++++++++++
more on employment and technology in this IMS blog
https://blog.stcloudstate.edu/ims?s=employment+technology
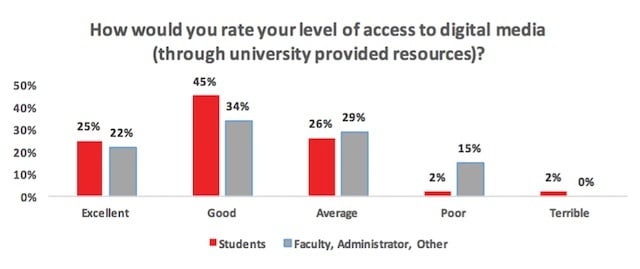
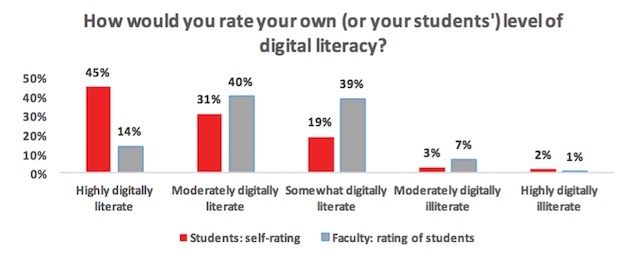
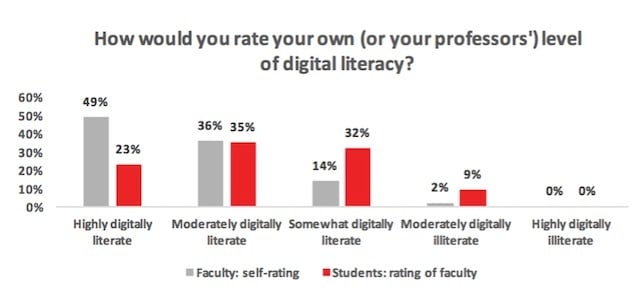
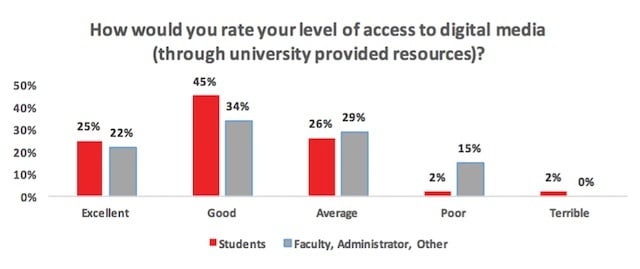
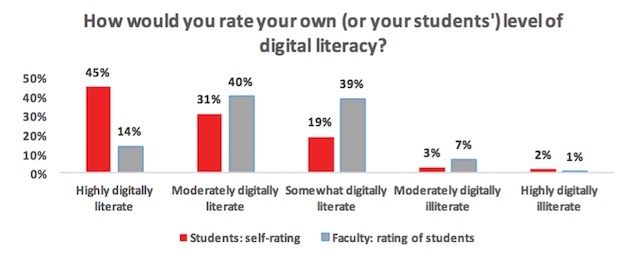
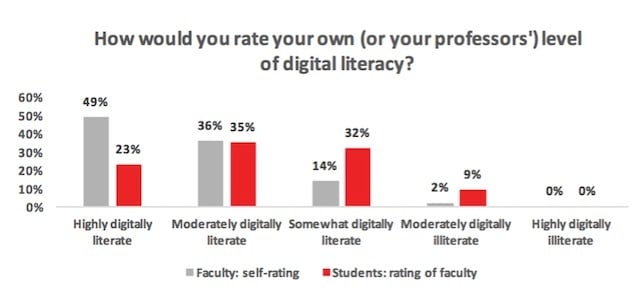
The 2016 State of Digital Media in Higher Education [Report]
Digital Literacy: Students and faculty disagree when evaluating their own
digital literacy competency vs. each other’s
4 Videos That Help Students & Parents Understand Financial Aid
http://www.freetech4teachers.com/2016/02/4-videos-help-students-parents.html
Choosing Financial Aid in a Nutshell from Planet Nutshell on Vimeo.
Borrow Wisely: FAFSA in a Nutshell from Planet Nutshell on Vimeo.
Understanding Federal Student Loans in a Nutshell from Planet Nutshell on Vimeo.
Federal vs. Private Student Loans in a Nutshell from Planet Nutshell on Vimeo.
http://www.educatorstechnology.com/
A Resource of educational web tools and mobile apps for teachers and educators
Q:
Hello,
I’m trying to log into D2L and am not able to. The user name and password that I’m using does work with my email. I had called yesterday and the individual I spoke with informed me that the professor needed to add me to a D2L list. I spoke with her (the professor) who told me she attempted to do this. Could you assist me with this issue?
A:
Login and password issue must be addressed with:
Free training videos. See http://mnscuims.mnscu.edu/training.html for links to the videos.
Version 10.1 Videos for Teachers
From Desire2Learn Community Site:
Content Overview
User Progress Overview
From Atomic Learning (free):
32 short videos–Content, User Progress, Discussions
From MnSCU:
Content Tool Changes in D2L Version 10.1
User Progress and Discussion Tool Changes in D2L Version 10.1
Version 10.1 Videos for Students
Overview Videos