Jan
2018
Meltdown and Spectre
Meltdown and Spectre
Bugs in modern computers leak passwords and sensitive data.
++++++
more on cybersecurity in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity
Digital Literacy for St. Cloud State University
Bugs in modern computers leak passwords and sensitive data.
++++++
more on cybersecurity in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity
How Not to be Hacked
Malware, Phishing, Hacking, Ransomware – oh my! Learn about the threats to you, your users and your library. During this session, we will explore the threats to online security and discuss solutions that can be implemented at any level. Most importantly, we will look at how we can educate our users on current threats and safety
Date: December 5th, 10AM
Presenter: Diana Silveira
Webinar December 5, 2017 10 AM
facebook.com/novarelibrary
twitter @Novarelibrary
+++++++++++
more on hacking in this IMS blog
https://blog.stcloudstate.edu/ims?s=hacker
The digital attack that brought Estonia to a standstill 10 years ago was the first shot in a cyberwar that has been raging between Moscow and the west ever since
It began at exactly 10pm on 26 April, 2007, when a Russian-speaking mob began rioting in the streets of Tallinn, the capital city of Estonia, killing one person and wounding dozens of others. That incident resonates powerfully in some of the recent conflicts in the US. In 2007, the Estonian government had announced that a bronze statue of a heroic second world war Soviet soldier was to be removed from a central city square. For ethnic Estonians, the statue had less to do with the war than with the Soviet occupation that followed it, which lasted until independence in 1991. For the country’s Russian-speaking minority – 25% of Estonia’s 1.3 million people – the removal of the memorial was another sign of ethnic discrimination.
That evening, Jaan Priisalu – a former risk manager for Estonia’s largest bank, Hansabank, who was working closely with the government on its cybersecurity infrastructure – was at home in Tallinn with his girlfriend when his phone rang. On the line was Hillar Aarelaid, the chief of Estonia’s cybercrime police.
“It’s going down,” Aarelaid declared. Alongside the street fighting, reports of digital attacks were beginning to filter in. The websites of the parliament, major universities, and national newspapers were crashing. Priisalu and Aarelaid had suspected something like this could happen one day. A digital attack on Estoniahad begun.
“The Russian theory of war allows you to defeat the enemy without ever having to touch him,” says Peter Pomerantsev, author of Nothing is True and Everything is Possible. “Estonia was an early experiment in that theory.”
Since then, Russia has only developed, and codified, these strategies. The techniques pioneered in Estonia are known as the “Gerasimov doctrine,” named after Valery Gerasimov, the chief of the general staff of the Russian military. In 2013, Gerasimov published an article in the Russian journal Military-Industrial Courier, articulating the strategy of what is now called “hybrid” or “nonlinear” warfare. “The lines between war and peace are blurred,” he wrote. New forms of antagonism, as seen in 2010’s Arab spring and the “colour revolutions” of the early 2000s, could transform a “perfectly thriving state, in a matter of months, and even days, into an arena of fierce armed conflict”.
Russia has deployed these strategies around the globe. Its 2008 war with Georgia, another former Soviet republic, relied on a mix of both conventional and cyber-attacks, as did the 2014 invasion of Crimea. Both began with civil unrest sparked via digital and social media – followed by tanks. Finland and Sweden have experienced near-constant Russian information operations. Russian hacks and social media operations have also occurred during recent elections in Holland, Germany, and France. Most recently, Spain’s leading daily, El País, reported on Russian meddling in the Catalonian independence referendum. Russian-supported hackers had allegedly worked with separatist groups, presumably with a mind to further undermining the EU in the wake of the Brexit vote.
The Kremlin has used the same strategies against its own people. Domestically, history books, school lessons, and media are manipulated, while laws are passed blocking foreign access to the Russian population’s online data from foreign companies – an essential resource in today’s global information-sharing culture. According to British military researcher Keir Giles, author of Nato’s Handbook of Russian Information Warfare, the Russian government, or actors that it supports, has even captured the social media accounts of celebrities in order to spread provocative messages under their names but without their knowledge. The goal, both at home and abroad, is to sever outside lines of communication so that people get their information only through controlled channels.
Tim Dowling Wednesday 29 November 2017 12.39 EST
According to its detractors, RT is Vladimir Putin’s global disinformation service, countering one version of the truth with another in a bid to undermine the whole notion of empirical truth. And yet influential people from all walks of public life appear on it, or take its money. You can’t criticise RT’s standards, they say, if you don’t watch it. So I watched it. For a week.
Suchet, the son of former ITV newsreader John Suchet and the nephew of actor David Suchet, has been working for RT since 2009. The offspring of well-known people feature often on RT. Sophie Shevardnadze, who presents Sophie & Co, is the granddaughter of former Georgian president and Soviet foreign minister Eduard Shevardnadze. Tyrel Ventura, who presents Watching the Hawks on RT America, is the son of wrestler-turned-politician Jesse Ventura. His co-host is Oliver Stone’s son Sean.
My note; so this is why Oliver Stone in his “documentary” went gentle on Putin, so his son can have a job. #Nepotism #FakeNews
RT’s stated mission is to offer an “alternative perspective on major global events”, but the world according to RT is often downright surreal.
Peter Pomerantsev, author of Nothing Is True and Everything Is Possible, about Putin’s Russia, and now a senior visiting fellow in global affairs at the London School of Economics, was in Moscow working in television when Russia Today first started hiring graduates from Britain and the US. “The people were really bright, they were being paid well,” he says. But they soon found they were being ordered to change their copy, or instructed how to cover certain stories to reflect well on the Kremlin. “Everyone had their own moment when they first twigged that this wasn’t like the BBC,” he says. “That, actually, this is being dictated from above.” The coverage of Russia’s war with Georgia in 2008 was a lightbulb moment for many, he says. They quit.
+++++++++++++++
more on Russian bots, trolls:
https://blog.stcloudstate.edu/ims/2017/11/22/bots-trolls-and-fake-news/
+++++++++++++++
more on state propaganda in this IMS blog
https://blog.stcloudstate.edu/ims/2017/11/21/china-of-xi/
http://www.express.co.uk/life-style/science-technology/870887/Bad-Rabbit-Ransomware-Malware-UK-Virus
Bill Brenner https://nakedsecurity.sophos.com/2017/10/24/bad-rabbit-ransomware-outbreak/
++++++++++++
more on cybersecurity in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity
From: Jodie Borgerding [mailto:Borgerding@amigos.org]
Sent: Wednesday, July 05, 2017 3:07 PM
To: Miltenoff, Plamen <pmiltenoff@stcloudstate.edu>
Cc: Nicole Walsh <WALSH@AMIGOS.ORG>
Subject: Proposal Submission for Privacy & Security Conference
Hi Plamen,
Thank you for your recent presentation proposal for the online conference, Privacy & Security in Today’s Library, presented by Amigos Library Services. Your proposal, The role of the library in teaching with technology unsupported by campus IT: the privacy and security issues of the “third-party,” has been accepted. I just wanted to confirm that you are still available to present on September 21, 2017 and if you have a time preference for your presentation (11 am, 12 pm, or 2 pm Central). If you are no longer able to participate, please let me know.
Nicole will be touch with you shortly with additional details and a speaker’s agreement.
Please let me know if you have any questions.
Thanks!
___________________
Jodie Borgerding Consulting & Education Services Manager Amigos Library Services 1190 Meramec Station Road, Suite 207 | Ballwin, MO 63021-6902 800-843-8482 x2897 | 972-340-2897(direct) http://www.amigos.org | borgerding@amigos.org
+++++++++++++++++
Bio
Dr. Plamen Miltenoff is an Information Specialist and Professor at St. Cloud State University. His education includes several graduate degrees in history and Library and Information Science and terminal degrees in education and psychology.
His professional interests encompass social media, multimedia, Web development and design, gaming and gamification, and learning environments (LEs).
Dr. Miltenoff organized and taught classes such as LIB 290 “Social Media in Global Context” (http://web.stcloudstate.edu/pmiltenoff/lib290/) and LIB 490/590 “Digital Storytelling” (http://web.stcloudstate.edu/pmiltenoff/lib490/) where issues of privacy and security are discussed.
Twitter handle @SCSUtechinstruc
Facebook page: https://www.facebook.com/InforMediaServices/
The virtuality of privacy and security on the modern campus:
The role of the library in teaching with technology unsupported by campus IT: the privacy and security issues of the “third-party software” teaching and learning
Abstract/Summary of Your Proposed Session
The virtualization reality changes rapidly all aspects of learning and teaching: from equipment to methodology, just when faculty have finalized their syllabus, they have to start a new, if they want to keep abreast with content changes and upgrades and engagement of a very different student fabric – Millennials.
Mainframes are replaced by microcomputers, microcomputers by smart phones and tablets, hard drives by cloud storage and wearables by IoT. The pace of hardware, software and application upgrade is becoming unbearable for students and faculty. Content creation and methodology becomes useless by the speed of becoming obsolete. In such environment, faculty students and IT staff barely can devote time and energy to deal with the rapidly increasing vulnerability connected with privacy and security.
In an effort to streamline ever-becoming-scarce resources, campus IT “standardizes” campus use of applications. Those are the applications, which IT chooses to troubleshoot campus-wide. Those are the applications recommended to faculty and students to use.
In an unprecedented burgeoning amount of applications, specifically for mobile devices, it is difficult to constraint faculty and students to use campus IT sanctioned applications, especially considering the rapid pace of such applications becoming obsolete. Faculty and students often “stray” away and go with their own choice. Such decision exposes faculty and students, personally, and the campus, institutionally, at risk. In a recent post by THE Journal, attention on campuses is drown to the fact that cyberattacks shift now from mobile devices to IoT and campus often are struggling even with their capability to guarantee cybersecurity of mobile devices on campus. Further, the use of third-party application might be in conflict with the FERPA campus-mandated policies. Such policies are lengthy and complex to absorb, both by faculty and students and often are excessively restrictive in terms of innovative ways to improve methodology and pedagogy of teaching and learning. The current procedure of faculty and students proposing new applications is a lengthy and cumbersome bureaucratic process, which often render the end-users’ proposals obsolete by the time the process is vetted.
Where/what is the balance between safeguarding privacy on campus and fostering security without stifling innovation and creativity? Can the library be the campus hub for education about privacy and security, the sandbox for testing and innovation and the body to expedite decision-making?
Abstract
The pace of changes in teaching and learning is becoming impossible to sustain: equipment evolves in accelerated pace, the methodology of teaching and learning cannot catch up with the equipment changes and atop, there are constant content updates. In an even-shrinking budget, faculty, students and IT staff barely can address the issues above, less time and energy left to address the increasing concerns about privacy and security.
In an unprecedented burgeoning amount of applications, specifically for mobile devices, it is difficult to constraint faculty and students to use campus IT sanctioned applications, especially considering the rapid pace of such applications becoming obsolete. Faculty and students often “stray” away and go with their own choice. Such decision exposes faculty and students, personally, and the campus, institutionally, at risk. In a recent post by THE Journal (https://blog.stcloudstate.edu/ims/2017/06/06/cybersecurity-and-students/), attention on campuses is drawn to the fact of cyberattacks shifting from mobile devices to IoT but campus still struggling to guarantee cybersecurity of mobile devices on campus. Further, the use of third-party applications might be in conflict with the FERPA campus-mandated policies. Such policies are lengthy and complex to absorb, both by faculty and students and often are excessively restrictive in terms of innovative ways to improve methodology and pedagogy of teaching and learning. The current procedure of faculty and students proposing new applications is a lengthy and cumbersome bureaucratic process, which often render the end-users’ proposals obsolete by the time the process is vetted.
Where/what is the balance between safeguarding privacy on campus and fostering security without stifling innovation and creativity? Can the library be the campus hub for education about privacy and security, the sandbox for testing and innovation and the body to expedite decision-making?
https://blog.stcloudstate.edu/ims/2017/06/06/cybersecurity-and-students/
Anything else you would like to add
3 take-aways from this session:
Re-examine the thin red line of the balance between standardization and innovation; between the need for security and privacy protection a
++++++++++++++
presentation:
https://www.slideshare.net/aidemoreto/the-virtuality-of-privacy-and-security-on-the
chat – slide 4, privacy. please take 2 min and share your definition of privacy on campus. Does it differ between faculty and students? what are the main characteristics to determine privacy
chat – slide 5, security. please take 2 min and share your definition of security on campus regarding electronic activities. Who’s responsibility is security? IT issue [only]?
poles: slide 6, technology unsupported by campus IT, is it worth considering? 1. i am a great believer in my freedom of choice 2. I firmly follow rules and this applies to the use of computer tools and applications 3. Whatever…
chat – slide 6, why third party applications? pros and cons. E.g. pros – familiarity with third party versus campus-required
pole, slide 6, appsmashing. App smashing is the ability to combine mobile apps in your teaching process. How do you feel about it? 1. The force is with us 2. Nonsense…
pole slide 7 third party apps and the comfort of faculty. How do you see the freedom of using third party apps? 1. All I want, thank you 2. I would rather follow the rules 3. Indifference is my middle name
pole slide 8 Technology standardization? 1. yes, 2. no, 3. indifferent
chat slide 9 if the two major issues colliding in this instance are: standardization versus third party and they have impact on privacy and security, how would you argue for the one or the other?
++++++++++++++++
notes from the conference
Speaker: Dr. Steve Albrecht – drsteve@drstevealbrecht.com
Dr. Steve Albrecht, author of Library Security: Better Communication, Safer Facilities, manages a training, coaching, and management consulting firm, using a dedicated and experienced team of subcontractor specialists. He is internationally known for his consulting and training work in workplace violence prevention training programs, school violence prevention, and high-risk human resources. Dr. Albrecht provides HR consulting, site security assessments, coaching, and training workshops in supervisory improvement, workplace violence prevention, harassment prevention, drug and alcohol awareness, team building, and more. He holds a B.A. in English, B.S. in Psychology, M.A. in Security Management, and a doctoral degree in Business Administration (D.B.A.). He has been a trainer for over 26 years and is a certified Professional in Human Resources (PHR), a Certified Protection Professional (CPP), a Board Certified Coach (BCC), and a Certified Threat Manager (CTM).
Session Description: Libraries don’t always need to hire a consultant to review the level of facility security. Using a structured assessment process, librarians can create a report that will help to make their building, staff, and patrons safer.
Chris Markman, MSLIS, MSIT Public Services Librarian Worcester Public Library
Measuring Library Vendor Cyber Security: Seven Easy Questions Every Librarian Can Ask
http://journal.code4lib.org/articles/11413
Bill Walker: http://www.amigos.org/innovating_metadata
+++++++++++++++
more on security in education in this IMS blog
https://blog.stcloudstate.edu/ims?s=security
more on privacy in education in this IMS blog
https://blog.stcloudstate.edu/ims?s=privacy
hackers can access your credit card data wirelessly, through something called radio frequency identification, or RFID
card has a tiny RFID sensor chip. These chips are supposed to make life easier by emitting radio signals for fast identification. The technology helps keep track of livestock and inventory. It makes automatic payment on toll roads and faster scanning of passports possible, and, starting around 2004, brought us contactless payment with certain credit cards.
REI and other companies sell a range of RFID-blocking products and say the number of customers looking for travel bags and credit card sleeves has been growing. That’s despite the fact that the percentage of credit cards with RFID chips in the U.S. is extremely small.
Still, people are worried about electronic pickpocketing — worried enough to strap on RFID-blocking fanny packs, even skinny jeans. In 2014, the San Francisco-based clothing company Betabrand partnered with Norton Security to create the first pair of denim with RFID protected pockets.
Eva Velasquez, president of the Identity Theft Resource Center, says from a consumer perspective, deciding whether to invest in RFID-blocking technology is all about evaluating risk. In the next few years, there will undoubtedly be millions more of these cards on the market.
if you’re worried about e-pickpocketing but don’t want to spend much money, you can make your own blocking wallet or wrap your cards or passport in a thick piece of aluminum foil. According to Consumer Reports, that works as well as most RFID protectors on the market.
+++++++++++++++
more on cybersecurity in this IMS blog
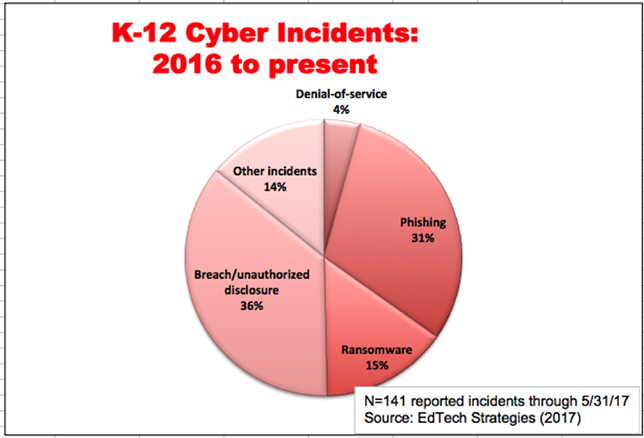
The creator of a national K–12 Cyber Incident Map warns that schools should act now, not later, to bolster their security.
By Richard Chang 06/08/17
https://thejournal.com/articles/2017/06/08/k12-cyber-incidents-have-been-increasing-in-2017.aspx
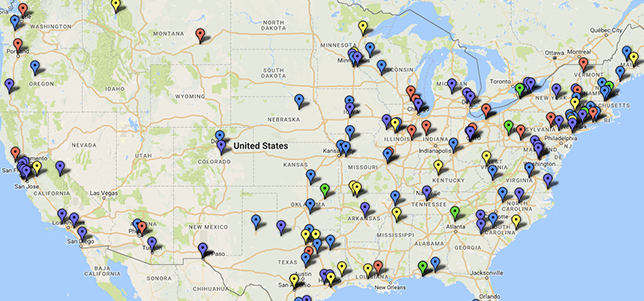
K–12 Cyber Incident Map , Doug Levin, president of Ed Tech Strategies
Levin has been tracking the publicly disclosed K–12 incidents on a color-coded map on his website, edtechstrategies.com. His sources include media reports, DataBreaches.net and the Privacy Rights Clearinghouse.
In a post published this week on the newly revamped Ferpa Sherpa education privacy site, Levin argues that not only have schools been “experiencing an increasing number of cyber incidents,” but “the range of cyber threats affecting schools appears to be diverse and shifting over time.”
concrete steps schools can take to improve their security, such as:
++++++++++++++++++++
more on cyber security in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity
By Rhea Kelly 06/05/17
https://campustechnology.com/articles/2017/06/05/survey-iot-overtakes-mobile-as-security-threat.aspx
a report from ISACA, a nonprofit association focused on knowledge and practices for information systems. The 2017 State of Cyber Security Study surveyed IT security leaders around the globe on security issues, the emerging threat landscape, workforce challenges and more.
++++++++++++++++++++++++++
By Sri Ravipati 06/09/17
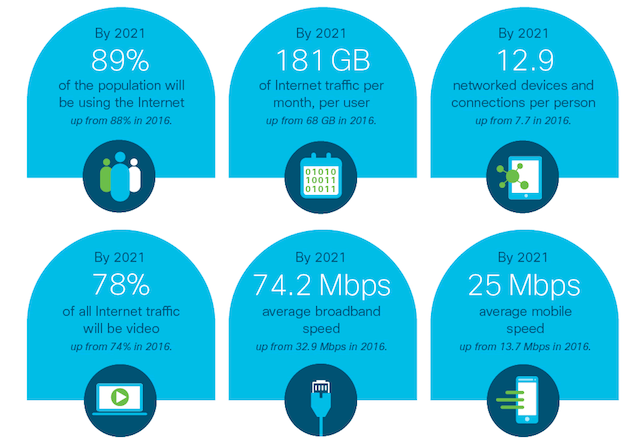
analysis comes from Cisco’s recent Visual Networking Index for the 2016-2021 forecast period.
To learn more, view the full report.
+++++++++++++++++++++++++++
+++++++++++++++++++++
https://blog.stcloudstate.edu/ims?s=internet+of+things
https://blog.stcloudstate.edu/ims?s=iot
By Richard Chang 04/04/17
Mobile learning is the top priority for K–12 IT leaders, according to the fifth annual K–12 IT Leadership Survey published by the Consortium for School Networking (CoSN).
It’s the first time mobile learning ranked as the highest priority in the survey. The No. 2 priority is broadband and network capacity, which ranked first last year, and the No. 3 priority is cybersecurity and privacy, with 62 percent of respondents rating them more important than last year.
CoSN is a nonprofit association for school system technology leaders. To read or download the full IT leadership survey, visit this CoSN site.
+++++++++++++++++++
more on mobile learning in this IMS blog
https://blog.stcloudstate.edu/ims?s=mobile+learning
By Sean D. Carberry Feb 23, 2017
https://fcw.com/articles/2017/02/23/critical-ceew-cyber-carbery.aspx
“Framework and Terminology for Understanding Cyber-Enabled Economic Warfare,” a new report by Samantha F. Ravich and Annie Fixler for the Foundation for Defense of Democracies.
Cyber-enabled economic warfare is a “hostile strategy involving attack(s) against a nation using cyber technology with the intent to weaken its economy and thereby reduce its political and military power.”
For example, China’s economic theft of intellectual property from the U.S. is considered CEEW, along with Russia’s cyberattack on Estonia and Iran’s Saudi Aramco attack. The authors also contend that the U.S. sanctions on Iran using cyber means to cut off Society for Worldwide Interbank Financial Telecommunication access also falls under CEEW.
http://www.defenddemocracy.org/content/uploads/documents/22217_Cyber_Definitions.pdf
+++++++++++++++++++
more on cybersecurity in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity