groups of learners
Group of Learners
https://www.pinterest.com/pin/470978073506744466/

Digital Literacy for St. Cloud State University
https://www.pinterest.com/pin/470978073506744466/

https://fiberlinkcorp.webex.com/fiberlinkcorp/onstage/g.php?d=358842843&t=a
Kayla Bittner 358 842 843 Twitter:#smartoffice
Android Wear (java)
Pebble (C)
Samsung Tizen (HTML5)
Apple Watch WatchKit (Swift, Objective-C support is buggy)
WatchKit is the least mature
limitations: no keyboard, no mouse, no touch screen, battery life, limited usable screen real estate, CPU performance
opportunities: hands-free, speech for text input, sensors (gyro, camera, accelerometer), gesture-based input, BLE (bluetoothSmart)
GOod wearable Design: Recognizes immediacy, leverages context of the wearer
challenging to develop good experiences for these devices.
802.11 will eat short battery life, in addition to bluetooth. Samsung Gear S will get notification even from afar, but usually smartwatch notification is paired only in immediate proximity of the bluetoothed device.
Addon –
industrial uses of wearable: tag and quickmessages, not occupying hands.
keyboard is with swipe gestures.
build in security is limited. Jailbroken / rooted devices are at higher risk> Open to hacking, still in infancy. No real MDM (Mobile Device Management) type solutions available
no management solutions exist today. OS: Tizen, Android, PebbleOS, Apple Watch OS etc
Cameras and other sensors cant be managed, monitored (spy scenario)
Is wearable an independent device or an extension of a smartphone
Best practices:
manage the connected device, not the wearable
be aware of what data can “leak” to a wearable device
if necessary, take more extreme measures (block bluetooth, ban devices)
new security options for mobile devices linked to wearables. bypass lock screen with presence of wearable, content sensitive security.
bricksimple.com
MaaS360.com/trial
Vanwynsberghe, H.., Boudry, E.., Verdegem, P.., & Vanderlinde, R.. (2014). Experts as facilitators for the implementation of social media in the library? A social network approach. Library Hi Tech, 32(3), 529-545. doi:10.1108/LHT-02-2014-0015
Excellent article. Apparently, they do things differently in Belgium.
“Social media literacy” (SML) can be defined as not only the practical
and critically cognitive competencies possessed by users of social media, but also the
motivation to employ these media effectively and appropriately for social interaction
and communication on the web (Vanwynsberghe and Verdegem, 2013).
Repeated by me numerous times, but ignored consistently.
p. 530 Therefore, the aim of this study is to empirically assess how a social media expert, or the employee with the most knowledge and skills concerning social media, in the library facilitates, or impedes, the information flow and implementation of social media in the library.
p. 541 The findings suggest that such social media experts play a significant role in either supporting or constraining the information flow and implementation of social media.
5.2 A social media expert plays an important role in the library for spreading
information about social media Unsurprisingly, social media experts are the most central actors for giving social media information; they share more social media information with other librarians and rarely receive information in return. Any information they do receive mostly comes from a person skilled in social media use. The social media expert as the central actor in the information network has the power to facilitate or prevent information exchange about social media (Scott and Carrington, 2012).
this is, if the experts are ALLOWED to participate. What if the social media access is usurped by very few others?
even worse, what if the social media is decentralized across?
link to this blog entry:
https://blog.stcloudstate.edu/ims/2015/02/18/digital-literacy-instruction-for-scsu-health-class/
short link: http://scsu.mn/1oaur7g
++++++++++++++++++++++++++
Your plan to develop presentation skills for this course:
+++++++++++++++++++++++++
It is tailored after the instructor’s requests.
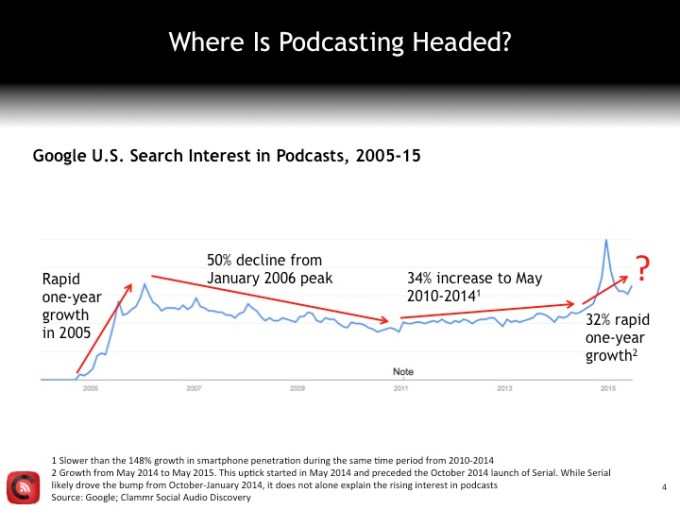
podcasting:
https://en.wikipedia.org/wiki/Podcast
http://techcrunch.com/2015/07/18/the-future-of-podcasting/
https://www.podomatic.com/login
=============
Multimedia Quizzes:
https://blog.stcloudstate.edu/ims/2016/02/13/4820/
==============
==============
==============
“Academic libraries are concerned about the digital literacy of their users but their programs continue to be focused on the information components defined by the President’s Commission on Information Literacy.” (p. 45)
Cordell, R. (2013). Library Instruction in the 21st Century. In: Rosanne, M (Ed.) Library Reference Services and Information Literacy: Models for Academic Institutions: Models for Academic Institutions. IGI Global.
More on digital literacy in this blog:
https://blog.stcloudstate.edu/ims/?s=library+digital+literacy
Thursday, February 19, 2015
Northrop — Best Buy Theater
Video game demos: 3-4:15pm
Discussion: 4:15-5:30pm
Join us for a discussion about the structural inequalities and prejudices present within the video games culture and industry from a variety of viewpoints. We will explore the ways underrepresented genders and races historically have been treated in technological sectors and how they are specifically manifested in video game culture. We will hear from scholars, students, and members of the broader community in the Twin Cities. Before the event, participate in a social exhibition of games made by students and local developers. Light refreshments will be provided.
http://ias.umn.edu/2015/02/19/games/
—
Amy Elizabeth Neeser
Research Services & Plant Sciences Librarian
Experts@Minnesota Communications Lead
University of Minnesota
85 Magrath Library
1984 Buford Ave | Saint Paul, MN 55108
(612) 624-7899
Horizon Report > 2015 Higher Education Edition
Key Trends Accelerating Technology Adoption in Higher Education 6
Long-Term Trends: Driving Ed Tech adoption in higher education for five or more years
> Advancing Cultures of Change and Innovation 8
> Increasing Cross-Institution Collaboration 10
Mid-Term Trends: Driving Ed Tech adoption in higher education for three to five years
> Growing Focus on Measuring Learning 12
> Proliferation of Open Educational Resources 14
Short-Term Trends: Driving Ed Tech adoption in higher education for the next one to two years
> Increasing Use of Blended Learning 16
> Redesigning Learning Spaces 18
Significant Challenges Impeding Technology Adoption in Higher Education 20
Solvable Challenges: Those that we understand and know how to solve
> Blending Formal and Informal Learning 22
> Improving Digital Literacy 24
Difficult Challenges: Those we understand but for which solutions are elusive
> Personalizing Learning 26
> Teaching Complex Thinking 28
Wicked Challenges: Those that are complex to even define, much less address
> Competing Models of Education 30
> Rewarding Teaching 32
Important Developments in Educational Technology for Higher Education 34
http://www.edudemic.com/what-comes-first-the-curriculum-or-technology/
The SAMR model, developed by Dr. Ruben Puentedura, represents the stages of tech integration: Substitution, Augmentation, Modification and Redefinition. This model challenges us to assess and reflect on not only how we integrate technology into our curriculum, but also how we modify, redefine and transform our classrooms through its use.
Integrating technology into the classroom can be exhilarating, fun, and at times a little scary. That said, I’ve often found that teachers are hungry for more information, and welcome the chance to bring new ideas to the classroom.
In the end, if teachers and their administration are ready to embrace the messiness and the risks that sometimes come with technology, the reward is that your school’s curriculum – which must be strong to start – can truly be taken to the next level, and beyond. Otherwise, we’ll all be still left trying to figure out how an abacus works.
Facebook was in the headlines last summer about their algorithm, when it came out that Twitter algorithm suggested the riots in Missouri in a very different way.
Facebook has been in the headline numerous times regarding their privacy issues
Who is holding a private company responsible about acts like this?Should it be hold responsible?
“The relationship between IT and the institution really needs to change if we’re going to use technology to address the fundamental issues that need to be addressed in higher education,” Grajek said. “Higher education leaders need to not just let their IT leaders do their own thing, help them fund some initiatives, but they really have to understand the potential of IT.”
Colleges and universities are searching for new talent in part to answer demands for new technologies while simultaneously offering core services such as user support, which Grajek described as the “new normal” for higher education IT offices.
“The CIO has grown from a hardware- or software-focused person in the basement of a building to a higher education executive who is expected to not only understand technology and be able to lead a large, complex and expensive department, but who also should be a first rate communicator who understands the business (and higher education) and can build relationships while implementing all of these projects,”