Mar
2021
Acer hit by ransomware attack
Computer giant Acer hit by $50 million ransomware attack
+++++++++++++++++
more on ransomware in this IMS blog
https://blog.stcloudstate.edu/ims?s=ransomware
Digital Literacy for St. Cloud State University
+++++++++++++++++
more on ransomware in this IMS blog
https://blog.stcloudstate.edu/ims?s=ransomware
How Not to be Hacked
Malware, Phishing, Hacking, Ransomware – oh my! Learn about the threats to you, your users and your library. During this session, we will explore the threats to online security and discuss solutions that can be implemented at any level. Most importantly, we will look at how we can educate our users on current threats and safety
Date: December 5th, 10AM
Presenter: Diana Silveira
Webinar December 5, 2017 10 AM
facebook.com/novarelibrary
twitter @Novarelibrary
+++++++++++
more on hacking in this IMS blog
https://blog.stcloudstate.edu/ims?s=hacker
http://www.reuters.com/article/us-adobe-systems-cyber-ransomware-idUSKCN0X502K
https://en.wikipedia.org/wiki/Ransomware
Ransomware is a type of malware that restricts access to the infected computer system in some way, and demands that the user pay a ransom to the malware operators to remove the restriction. Some forms of ransomware systematically encrypt files on the system’s hard drive, which become difficult or impossible to decrypt without paying the ransom for the encryption key, while some may simply lock the system and display messages intended to coax the user into paying. Ransomware typically propagates as a trojan, whose payload is disguised as a seemingly legitimate file.
Kim Boatman
http://us.norton.com/yoursecurityresource/detail.jsp?aid=rise_in_ransomware
America’s schools increasingly face costly cybersecurity risks, yet many systems are ill-prepared for the challenge. #EWOpinion #RHSU https://t.co/TQKkhiEdqI
— Education Week (@educationweek) January 27, 2022
As of this past August, Politico has reported that ransomware attacks have hit 58 education organizations and school districts, including 830 individual schools. Last March, the Broward County, Fla., district didn’t pay a $40 million ransom, leading the hackers to publish 26,000 stolen files online (these included student and staff Social Security numbers and addresses).
+++++++++++++
more on cybersecurity in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity
In what is currently a fragmented regulatory and standards landscape internationally, the EU has taken strongest interest in IoT, but from a competition perspective. The EU Commission is investigating competition questions related especially to the three dominant voice-assistants (Alexa, Google Assistant, Siri), a node for issues of data privacy and interoperability. Its recently released report hardly mentions security.
+++++++++++++++++
more on IoT in this iMS blog
https://blog.stcloudstate.edu/ims?s=internet+of+things
a historic report last week from the nation’s top boss of counterintelligence.
the need for the United States to order the closure of the Chinese government’s consulate in Houston.
metaphor for this aspect of the spy game: a layer cake.
There’s a layer of activity that is visible to all — the actions or comments of public figures, or statements made via official channels.
Then there’s a clandestine layer that is usually visible only to another clandestine service: the work of spies being watched by other spies.
Counterintelligence officials watching Chinese intelligence activities in Houston, for example, knew the consulate was a base for efforts to steal intellectual property or recruit potential agents
And there’s at least a third layer about which the official statements raised questions: the work of spies who are operating without being detected.
The challenges of election security include its incredible breadth — every county in the United States is a potential target — and vast depth, from the prospect of cyberattacks on voter systems, to the theft of information that can then be released to embarrass a target, to the ongoing and messy war on social media over disinformation and political agitation.
Witnesses have told Congress that when Facebook and Twitter made it more difficult to create and use fake accounts to spread disinformation and amplify controversy, Russia and China began to rely more on open channels.
In 2016, Russian influencemongers posed as fake Americans and engaged with them as though they were responding to the same election alongside one another. Russian operatives even used Facebook to organize real-world campaign events across the United States.
But RT’s account on Twitter or China’s foreign ministry representatives aren’t pretending to do anything but serve as voices for Moscow or Beijing.
the offer of a $10 million bounty for information about threats to the election.
+++++++++++++++++++
more on trolls in this IMS blog
https://blog.stcloudstate.edu/ims?s=troll
1. Link Security
From ransomware to phishing and other types of security breaches, direct contact is the number one way that you can create a vulnerability in your system. Those who commit these online crimes are finding smarter and sneakier ways to infiltrate your data every day. Sometimes the attack can even come as an email from a legitimate sender, or appear to be a perfectly normal message on social media. The goal is usually to get you to click on a link.
Solution: Make sure the security preferences for your email account(s) are set up to filter spamming, phishing and executable files that aren’t recognized.
2. Unknown Devices
Solution: Your IT system should include a solution that tracks all devices, including those not owned by your school, that enter the network.
3. Out of Date Technology
Contrary to popular misconception, user interaction isn’t always required for a cyber attack to be launched. The WannaCry attack targeted hundreds of computers all with the same security vulnerability on their Windows operating systems.
Solution: Again, an IT solution that tracks all devices is important, but one that can also check on software upgrades and block access to certain apps is ideal.
4. User Error
A data breach in Florida is just one example of the chaos user error can provoke. This issue didn’t begin with hackers at all. It began with carelessness that caused sensitive information to become public.
User error occurs regularly, and a common root of this is failing to restrict access to files or certain sites that may be compromised.
Solution: Restrict user access to sensitive documents only to those who absolutely need them, and make sure that your site architecture is set up to require a secure login for access. You may also want to create a white list of safe sites and applications and block the rest.
5. No Backup
As disheartening as it sounds, even when you take all the necessary precautions to protect your vital information, data breaches can still occur. When an attack happens, it’s often a major blow to productivity to try and get all the information back into a secure place. Worse, vital work can be lost for good.
Solution: Install a backup system on each school device that sends data to a remote server throughout the day (not just at night) to help make sure nothing is lost.
+++++++++++++++
more on cybersecurrity in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity
http://www.express.co.uk/life-style/science-technology/870887/Bad-Rabbit-Ransomware-Malware-UK-Virus
Bill Brenner https://nakedsecurity.sophos.com/2017/10/24/bad-rabbit-ransomware-outbreak/
++++++++++++
more on cybersecurity in this IMS blog
https://blog.stcloudstate.edu/ims?s=cybersecurity
By Rhea Kelly 06/05/17
https://campustechnology.com/articles/2017/06/05/survey-iot-overtakes-mobile-as-security-threat.aspx
a report from ISACA, a nonprofit association focused on knowledge and practices for information systems. The 2017 State of Cyber Security Study surveyed IT security leaders around the globe on security issues, the emerging threat landscape, workforce challenges and more.
++++++++++++++++++++++++++
By Sri Ravipati 06/09/17
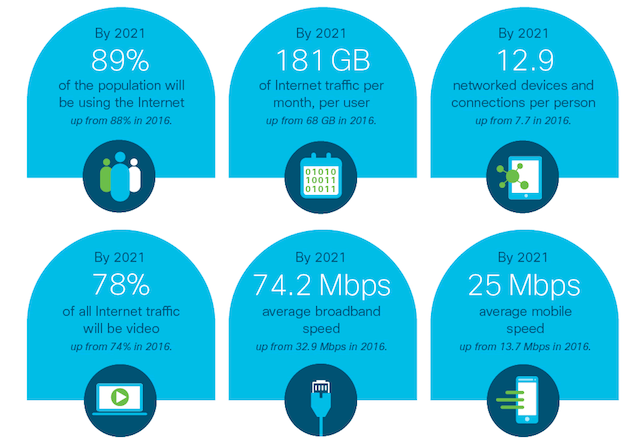
analysis comes from Cisco’s recent Visual Networking Index for the 2016-2021 forecast period.
To learn more, view the full report.
+++++++++++++++++++++++++++
+++++++++++++++++++++
https://blog.stcloudstate.edu/ims?s=internet+of+things
https://blog.stcloudstate.edu/ims?s=iot